Last Friday, widely used websites like PayPal, Netflix and Twitter were unavailable due to a distributed denial of service (DDOS) attack . Hackers got into those systems through technical holes in hundreds of thousands of personal wifi-enabled devices like baby monitors and personal devices to bring down a website host, Dyn. For people in healthcare who are concerned about security, it brought a system vulnerability into sharp relief.
I am not a computer expert (disclaimer), but as I understand it, many of the consumer and even medical personal devices that we use to monitor our health and deliver data to the electronic patient record are pre-set with default passwords. Users don’t usually reset them to a private password so most of these IoT devices remain set with the factory default. Apparently, any hacker can guess the default passwords, hijack the devices and get them to log into a web host system like Dyn all at once which overloads the system with requests and causes it to fail.
Vulnerabilities to Healthcare Organizations and Individual Patients
These kinds of vulnerabilities pose risks to individual patients and healthcare systems.
Healthcare organizations have already sustained several debilitating attacks that have occurred in this way. In 2014, Boston Children’s Hospital was offline for several days after a DDOS attack by the group Anonymous that was protesting its treatment of a patient; other hospitals have sustained similar attacks. Computer experts say there are measures that hospitals and health systems can institute to prevent such attacks. This article broadly describes some of those precautions.
Concerns regarding the safety of individual patient devices such as heart monitors and insulin pumps fall into two broad categories 1) diverting data thus compromising patient privacy and 2) resetting dosing parameters thus endangering patient lives. The FDA, which regulates medical devices, is interested in the issue and has studied it, but so far has decided not to regulate the IoT of medical devices for several reasons. It is technically difficult to do, technology and security advance more quickly than threats, and the threat to individual patient health and safety is more theoretical than actual. A hacker could hack into an individual patient’s medical device to reset it, but that is very unlikely. It doesn’t mean that patients with consumer or medical devices cannot or should not take steps to protect themselves. Patients can reset default passwords. This article from TechTarget describes the pros and cons of patient access to device passwords in more detail.
Due Diligence
The attack last week wasn’t a state-sponsored attack from Russia as originally postulated, but came from non-state-sponsored vulnerabilities out of China .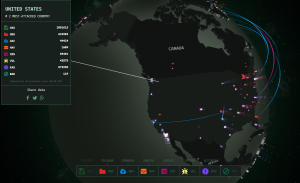 No matter where it came from, last week’s incident reminds everyone, including those in healthcare, that a damaging hack attack is not that hard to do. In fact, attacks like this occur all the time, all over the globe. For a little fun – or for a wake-up call – check out this website where you can watch cyberattacks in real time. There is usually a lot of activity into and out of the U.S., Russia and China.
No matter where it came from, last week’s incident reminds everyone, including those in healthcare, that a damaging hack attack is not that hard to do. In fact, attacks like this occur all the time, all over the globe. For a little fun – or for a wake-up call – check out this website where you can watch cyberattacks in real time. There is usually a lot of activity into and out of the U.S., Russia and China.
The challenge for IT specialists in health care is to make sure these attacks aren’t perpetrated on your patients or your organization. This article from Modern Healthcare describes Athenahealth and Allscripts outages that occurred during the DDOS attack last week. A Medical Group Management Association health information expert reminded individual physicians’ offices that their data, too, can be taken offline during an attack and he recommends backup plans that involve having a technician on speed dial.
An article out of the 2014 Black Hat hackers conference explains that all attacks –even those not directly targeted at healthcare – should be of concern to health IT professionals.
All hacks and cyberattacks can expose your patients and organizations. The Dyn DDOS attack is a reminder to do your due diligence.
Pingback: Health Wonk Review: The Game 7 of Politics Edition | Wright on Health